What Is an ISP Proxy? And How to Use It Safely for Multi-Account Management
Managing multiple accounts today isn’t just about creating more profiles—it’s about staying undetected.
Whether you're running stores on Amazon, scaling TikTok accounts, or doing affiliate marketing, your setup is only as strong as your proxy—especially when using an antidetect browser.
One wrong IP choice can lead to account bans, verification loops, or even complete shutdowns.
In this guide, we’ll break down what ISP proxies are, how they work, and how to use them safely with tools like Hidemium.
What Is an ISP Proxy?
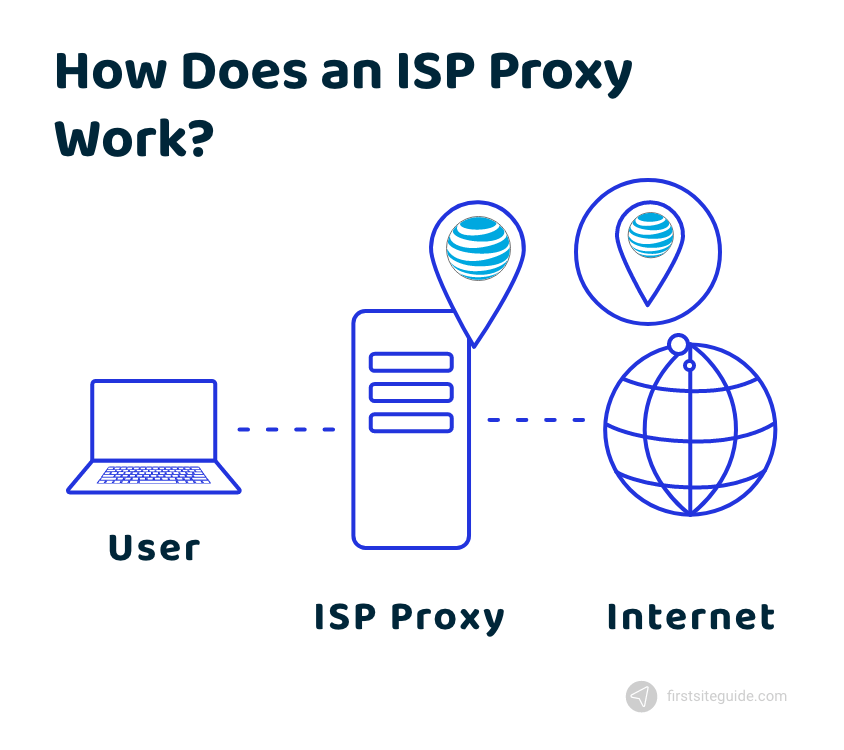
An ISP proxy (Internet Service Provider proxy) is a type of proxy that combines:
- The speed of datacenter proxies
- The trust level of residential IPs
In simple terms, ISP proxies are real IP addresses issued by Internet Service Providers, but hosted on high-performance servers.
Why does that matter?
Because platforms like Facebook, Amazon, or Google tend to trust residential IPs more than datacenter ones.
👉 ISP proxies give you:
- Fast connection speed
- Stable performance
- Lower risk of being flagged
Why ISP Proxies Matter for Multi-Account Users
If you're managing multiple accounts, platforms are constantly looking for signals like:
- IP address
- Device fingerprint
- Location
- Browser behavior
If multiple accounts share similar data → they get linked → and eventually banned.
This is where ISP proxies come in
Using ISP proxies allows you to:
- Assign a unique IP per account
- Maintain consistent identity per profile
- Reduce the risk of account linkage
👉 When combined with Hidemium, each account runs in a fully isolated environment:
- Separate browser profile
- Unique fingerprint
- Dedicated proxy
Common Use Cases of ISP Proxies
ISP proxies are widely used in:
🔹 Multi-account management
Run multiple Facebook, Amazon, TikTok, or Gmail accounts safely without cross-linking.
🔹 Web scraping
Collect data at scale while avoiding rate limits and IP bans.
🔹 Affiliate marketing
Manage multiple ad accounts or landing pages across regions.
🔹 Ad testing & automation
Simulate different user environments to test campaigns.
Can ISP Proxies Hide You From Your ISP?
Short answer: No, not completely.
Your ISP can still detect that you’re using a proxy.
However, what matters more is:
👉 Websites cannot see your real IP
This means:
- Your identity is hidden from platforms
- Your activity appears as coming from a different user
When using Hidemium:
- Your IP + fingerprint + environment are all aligned
- This makes detection much harder for platforms
Can ISPs Detect or Block Proxies?
Yes, especially if you use:
- Free proxies
- Public/shared IPs
- Low-quality proxy providers
These can lead to:
- IP bans
- Slow performance
- Suspicious activity flags
How to Use ISP Proxies Without Getting Blocked
To stay safe, follow these best practices:
✅ 1. Use high-quality ISP proxies
- Clean IP history
- Dedicated or low-share IPs
- Location targeting
✅ 2. Assign one proxy per account
Never reuse the same IP across multiple accounts.
✅ 3. Combine with an antidetect browser
Using only proxies is not enough.
With Hidemium, you can:
- Create isolated browser profiles
- Customize fingerprints (OS, timezone, language…)
- Attach a unique proxy to each profile
👉 This creates a complete digital identity per account
✅ 4. Avoid free or overused proxies
They are the fastest way to get banned.
Should You Create Your Own ISP Proxies?
Technically possible—but not practical.
You would need:
- IP leasing from ISPs
- Server infrastructure
- Network configuration
👉 For most users, this is:
- Expensive
- Complex
- Time-consuming
✔️ The better option: buy from trusted providers and integrate with Hidemium
Final Thoughts
ISP proxies are one of the most reliable solutions for managing multiple accounts safely.
But proxies alone are not enough.
To truly avoid detection, you need a complete setup:
- Clean IP (ISP proxy)
- Unique browser fingerprint
- Isolated environment per account
👉 That’s exactly where Hidemium comes in.
By combining ISP proxies with advanced fingerprint control and profile isolation, you can scale your operations with confidence—without worrying about bans or account linkage.
Related Blogs
Are you suddenly unable to withdraw, deposit, or access your cryptocurrency wallet on Coinbase? There’s a good chance your account has been restricted. This is not uncommon: some users are flagged after small transactions, while others can have their accounts locked for weeks – even after completing identity verification and contacting support. What’s most frustrating is that you’ll often only[…]
BestProxy: The world's leading high-quality proxy server In today’s data-driven business environment, companies conducting market research, advertising campaigns, or large-scale data collection often rely on proxy services to avoid detection and potential bans by platforms. However, traditional proxy providers frequently suffer from unstable connections and limited geographic coverage, reducing[…]
In the field of affiliate marketing, cookie stuffing is a common form of fraud. This occurs when tracking cookies are installed on users' devices.without their knowledge. This allows fraudsters to receive commissions for actions they didn't actually commit.The consequences extend beyond just lost costs. Businesses also face issues such as inaccurate marketing data, unreliable performance reports,[…]
Google Chrome is a popular browser but not the best choice when you need Manage Multiple X Accounts (Twitter) at the same time. In this article, we will explore the limitations of Chrome, the role of browser fingerprint, and why antidetect browser Hidemium is a superior solution for creating and operating multiple secure accounts.1. Is it possible to create multiple X accounts on[…]
In the digital age, owning multiple Gmail accounts is not only a personal need but also a vital factor for people MMO (Make Money Online), marketers or YouTubers. However, mass Gmail registration is often subject to Google checkpoints, requires complex verification and is easily locked. So what is the tool that helps you create mass Gmail safely, avoid checkpoints and save time in 2025?In this[…]







