In today's internet environment, managing digital identity is becoming increasingly important. Every time you access a website, log into an account, or perform an online action, you leave behind certain identifying marks. The collection of this data forms a digital identity digital footprint, which many platforms use to identify and track users.
One of the popular tools used to analyze this level of recognition is Iphey. This tool allows you to check how your browser and system display information on websites, helping you understand what information is being exposed. In this article, you'll find detailed, step-by-step instructions on how to pass Iphey's checks using a browser that avoids detection.Hidemium helps enhance privacy and security when operating online.
1. What is Iphey?
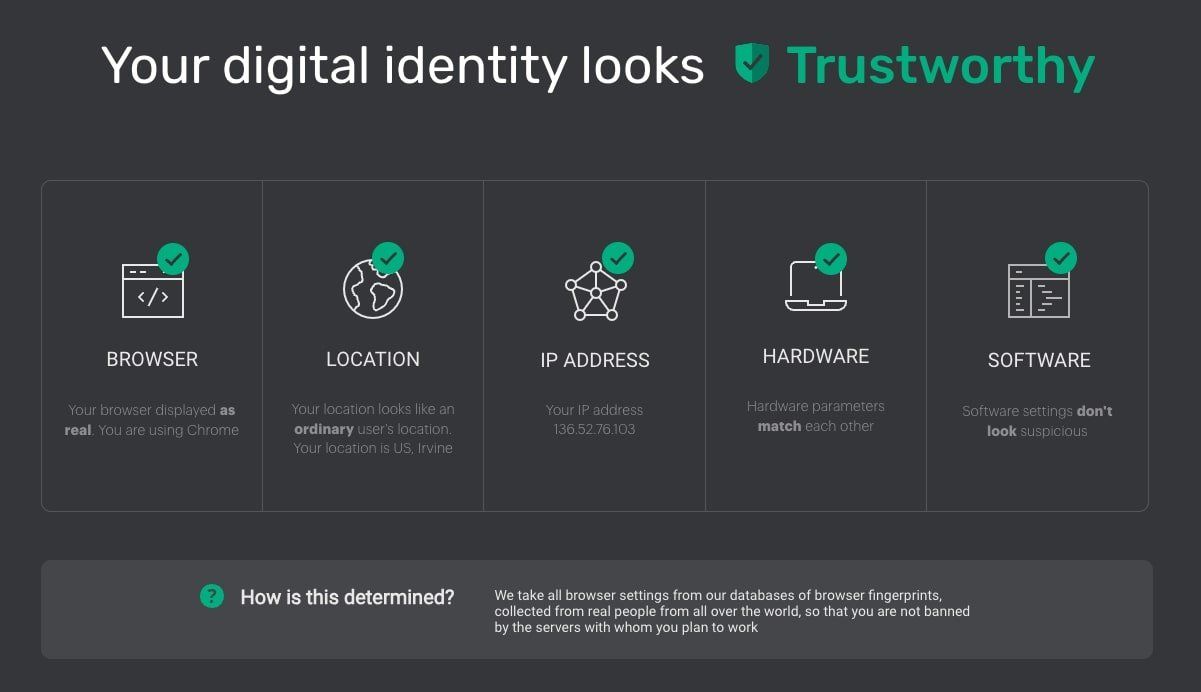
Iphey is a browser fingerprint analysis tool that helps users understand how their system is identified on the internet. This platform checks various factors, from IP addresses and browser configurations to detailed device specifications.
By collecting and analyzing this data, Iphey creates a comprehensive “snapshot” of your digital identity when browsing the web. This information helps detect potential security vulnerabilities or signs that could make your accounts vulnerable to tracking or linking.
Passing Iphey's tests is often seen as an indicator that your online identity is properly established, consistent, and more secure when using the internet.
>>> Learn more: What is Canvas Fingerprinting? - The latest online tracking technology.
2. Why is passing the Iphey test important?
The ability to pass the tests Iphey These are considered a de facto standard for those working in security, privacy, or web development. When your system passes these checks, it indicates that your browser and network configurations are functioning properly natural and consistent, just like a regular user.
This is especially important because many online platforms now use fingerprint analysis techniques to detect unusual behavior. If browser or network configurations show signs of irregularities, the system can flag the account, restrict activity, or even block access.
Therefore, for those who want to manage their digital identity professionally—such as in online marketing, managing multiple accounts, or data research—understanding and passing Iphey's checks is a crucial step in maintaining stability and security while operating online.
>>> Learn more: What is a Digital Footprint? Understanding your online presence correctly.
3. Important fingerprint features that need to be concealed to bypass Iphey
To pass the test of IpheyYou need to control many different identification factors, not just the IP address. Although IP is the most easily identifiable data, the deciding factor often lies in...Consistency across multiple specifications.
Iphey is designed to detect inconsistencies between these data points. Some key elements include:
IP address and connection type
iPhey identifies your current IP address and analyzes the type of connection being used. This tool can also detect the use of proxies or anonymity solutions if the network configuration shows signs of abnormality.
Browser and system information
Data such as browser version, operating system, screen resolution, or device configuration are all recorded. This information is then compared to see if it is reasonable and appropriate for the actual user environment.
Advanced fingerprint technology
In addition to basic parameters, Iphey also uses several advanced analytical methods to create detailed equipment profiles, including:
output analysisHTML5 Canvas API
query testingDNS
Evaluate hardware characteristics throughWebGL
This data can reveal subtle differences between the actual configuration and the simulated configuration, making it easier for the system to detect your settings.
4. Hidemium: An effective solution to pass the Iphey test.
4.1 Why do you need a browser that avoids detection to bypass Iphey?
Basic tools like proxies can only change your IP address, but they can't completely hide your digital fingerprint. With advanced verification systems like...IpheySimply changing the IP address is not enough.
Although proxies can act as an intermediary for network connections, your browser continues to send other information such as system configuration, hardware characteristics, graphics data, and browser settings. When this data is inconsistent with your IP address or network environment, analytics tools can quickly detect anomalies.
That's why many experts choose to use it.browser anti-detectionThese tools not only change IP addresses but also have the ability to adjust and simulate various system parameters, helping to create a complete and consistent browser identity.
A typical example isHidemiumThe browser is designed to minimize browser fingerprints and help users manage their digital identity more effectively.
4.2 What makes Hidemium such a powerful tool?
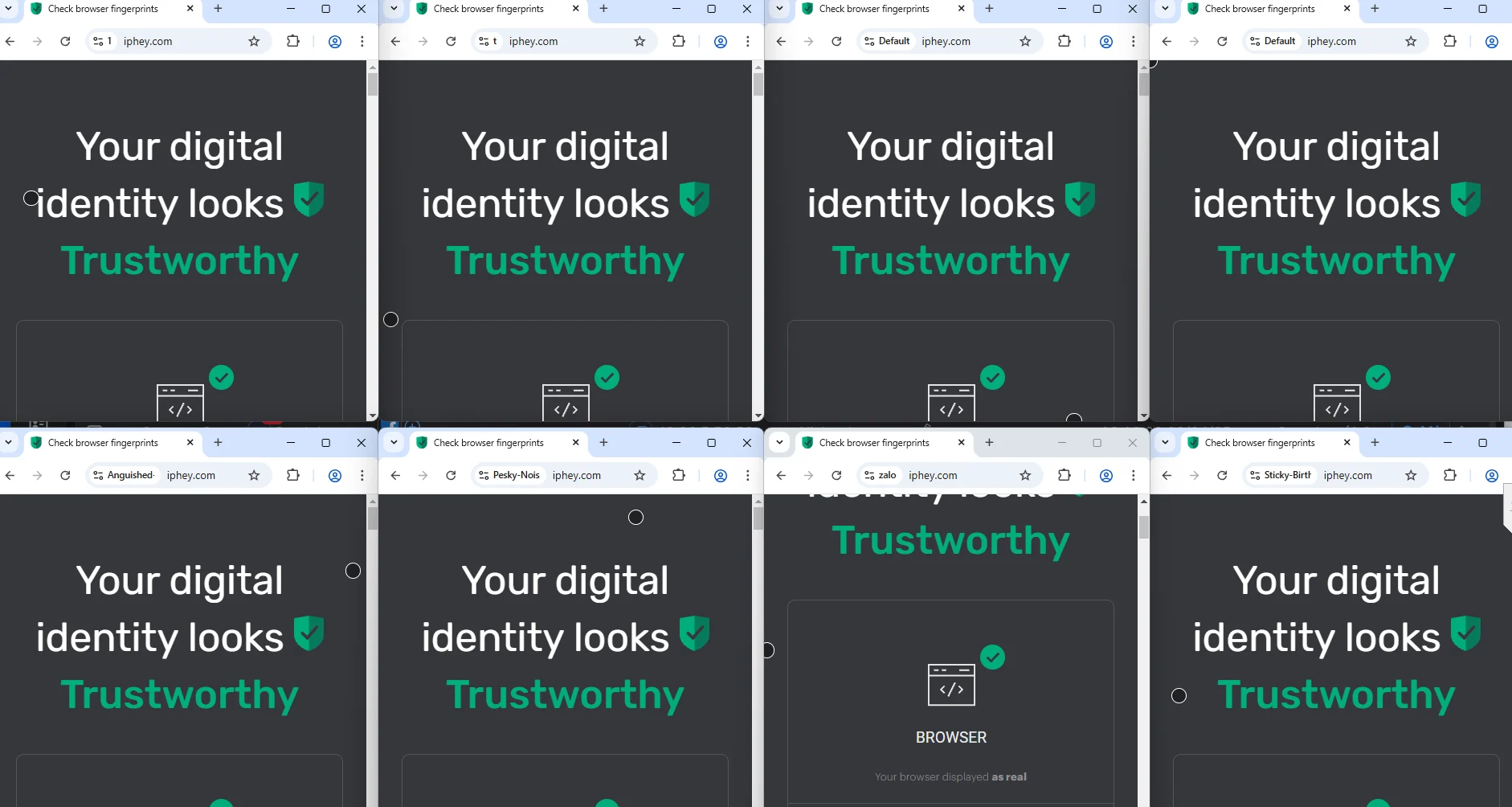
One of the outstanding strengths ofHidemiumThis allows you to create and manage multiple independent browser profiles. Each profile is configured as a separate device environment with a different browser fingerprint.
As a result, users can:
Create multiple separate digital identities.
Switch between browser profiles without linking data.
Maintain consistency between IP address, system configuration, and browser fingerprint.
This level of detail control is particularly useful in online activities requiring a high degree of privacy, such as managing multiple accounts, online transactions, or web data research.
When properly configured, profiles in Hidemium can help the browser environment appear more natural when inspected by analytics tools like Iphey, thereby reducing the risk of being detected or flagged as anomalous.
>>> Learn more:Fingerprint recognition when using Antidetect Browser software.
5. Conclude
In the context of increasingly intelligent detection systems, managing browser fingerprints and digital identities has become crucial for anyone who frequently uses the internet. Verification tools such asIpheyThis helps users understand the information their browser is revealing, allowing them to identify weaknesses in their privacy settings.
To consistently pass these tests, simply changing the IP address is not enough. Users need to ensure the following:Consistency between IP address, browser configuration, and system parameters.This is why anti-detection browsers are becoming increasingly popular.
With the ability to create multiple independent browser profiles and fine-tune device fingerprint recognition,HidemiumIt helps users build a safer and more private browsing environment. Whether you're managing multiple accounts, researching data, or simply want to protect your online identity, setting up the right tools will significantly reduce the risk of being tracked or detected.
Take proactive control of your digital footprint today to ensure a safer and more sustainable internet experience.
👉 Hidemium currently offers a 3-day free trial with 1000 profiles – the perfect choice to start your journey of identity protection and safe web browsing.Download and experience it today!
Related Blogs
You are looking for answers to the question “What is SD-WAN?”and why is this technology increasingly mentioned in the context of digital transformation? Whether you are a system administrator, business owner or simply someone interested in optimizing network systems, this article from Hidemium AntiDetect Browser will help you understand SD-WAN technology and the value it brings to your[…]
In the era of digital data explosion, the need to collect and process information from the Internet is becoming increasingly urgent. This is the time Web Scraping Serves as a powerful alternative to time-consuming and resource-intensive manual data collection methods.So What is Web Scraping? How does it work and what value does it bring to individuals or businesses? Let's find out Hidemium[…]
Are you looking to rent a proxy for use on Facebook, Amazon, Instagram, Shopify, or other platforms? Proxies are not just tools for anonymous access but also help you perform tasks such as data scraping, running ads, or managing multiple accounts effectively. However, each platform has different requirements when it comes to proxy usage. BestProxy, a global proxy service with over 80 million[…]
What is Niche Scraper And is this the right tool to start dropshipping? That is the question that many new dropshippers ask when trying to find potential products to sell. In the journey of starting an online business, choosing the right product research tool from the beginning can determine the speed of orders and the ability to maintain profits. Niche Scraper is one of the names mentioned a[…]
AdGuard DNS is a free DNS service designed to block intrusive ads and protect your devices from online threats. Instead of using the default DNS servers provided by your internet service provider, you can switch to AdGuard DNS to filter malicious content right from the first connection. This not only enhances your browsing speed but also improves your online privacy and security.In this[…]
In the digital age, Artificial Intelligence (AI) is becoming an indispensable assistant across many fields, especially in automating workflows. Among the most notable is ChatGPT – a natural language processing AI model developed by OpenAI. Not only can it engage in conversations, but it can also understand and execute complex requests in text form.So, what is ChatGPT? And how can it be applied to[…]



.png)



